One key to rule them all: Recovering the master key from RAM to break Android's file-based encryption - ScienceDirect

One key to rule them all: Recovering the master key from RAM to break Android's file-based encryption - ScienceDirect

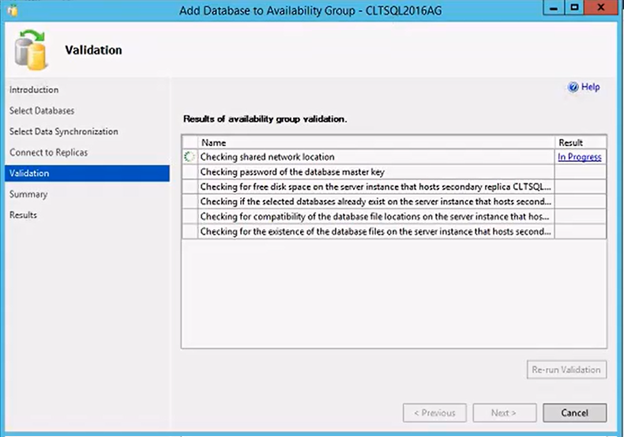
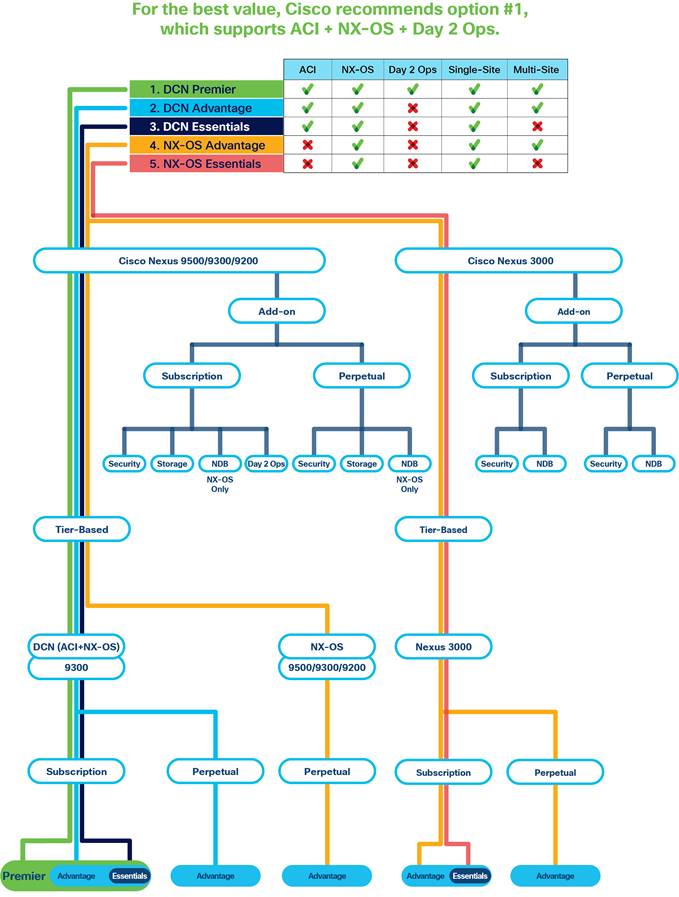
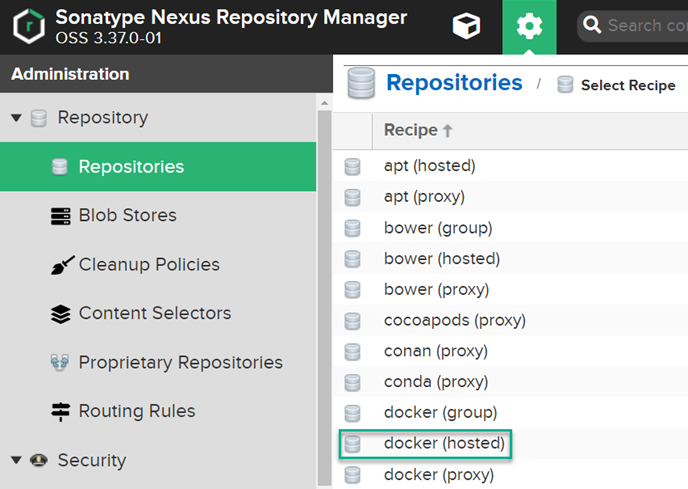
Introduction To Cisco Nexus Dashboard And Installation, Integrating With Radius, Configuring Intersight And Site Onboarding -
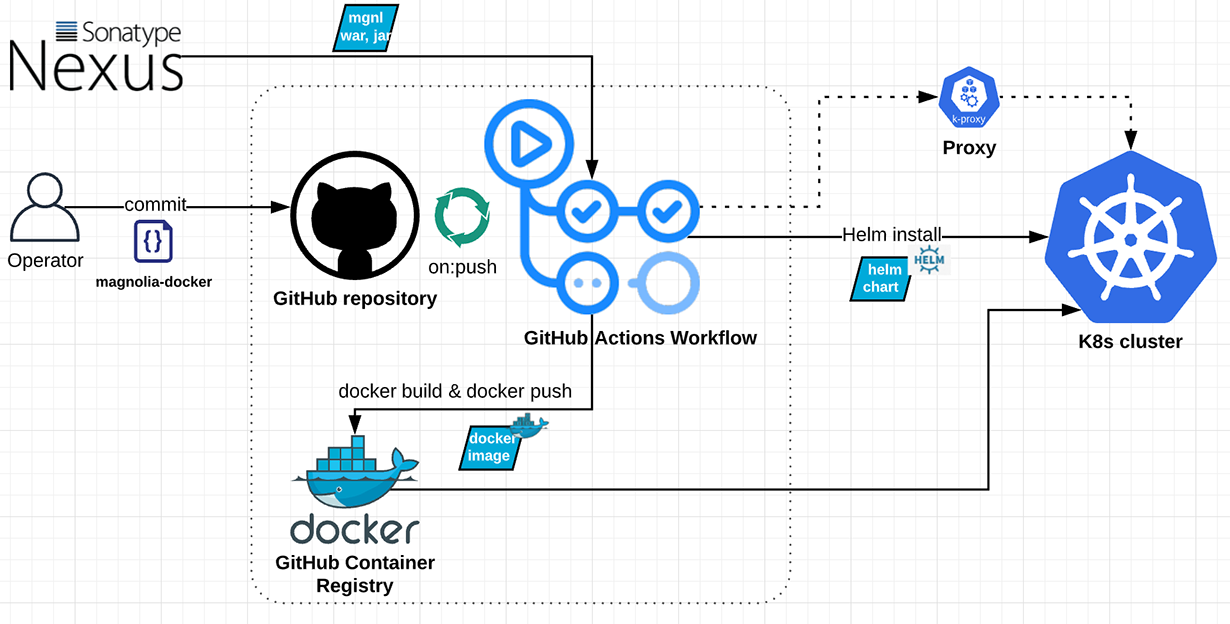
Building a Continuous Delivery Pipeline with GitHub and Helm to deploy Magnolia to Kubernetes | Magnolia Headless CMS
How to fix my Nexus plugin on FL Studio if it says there is an unknown error and my sounds won't play anymore - Quora
![PDF] One key to rule them all: Recovering the master key from RAM to break Android's file-based encryption | Semantic Scholar PDF] One key to rule them all: Recovering the master key from RAM to break Android's file-based encryption | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/19f6602b16479356f2767cf3837c9eacaa186222/8-Figure4-1.png)
PDF] One key to rule them all: Recovering the master key from RAM to break Android's file-based encryption | Semantic Scholar
![PDF] One key to rule them all: Recovering the master key from RAM to break Android's file-based encryption | Semantic Scholar PDF] One key to rule them all: Recovering the master key from RAM to break Android's file-based encryption | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/19f6602b16479356f2767cf3837c9eacaa186222/7-Table1-1.png)
PDF] One key to rule them all: Recovering the master key from RAM to break Android's file-based encryption | Semantic Scholar



![Cisco Nexus Dashboard User Guide, Release 2.2.x - Troubleshooting [Cisco Nexus Dashboard] - Cisco Cisco Nexus Dashboard User Guide, Release 2.2.x - Troubleshooting [Cisco Nexus Dashboard] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/500001-600000/500001-510000/adoc/503639.jpg)