Processing time to compute HMAC-SHA-256 and HMAC-SHA-384 with keys of... | Download Scientific Diagram
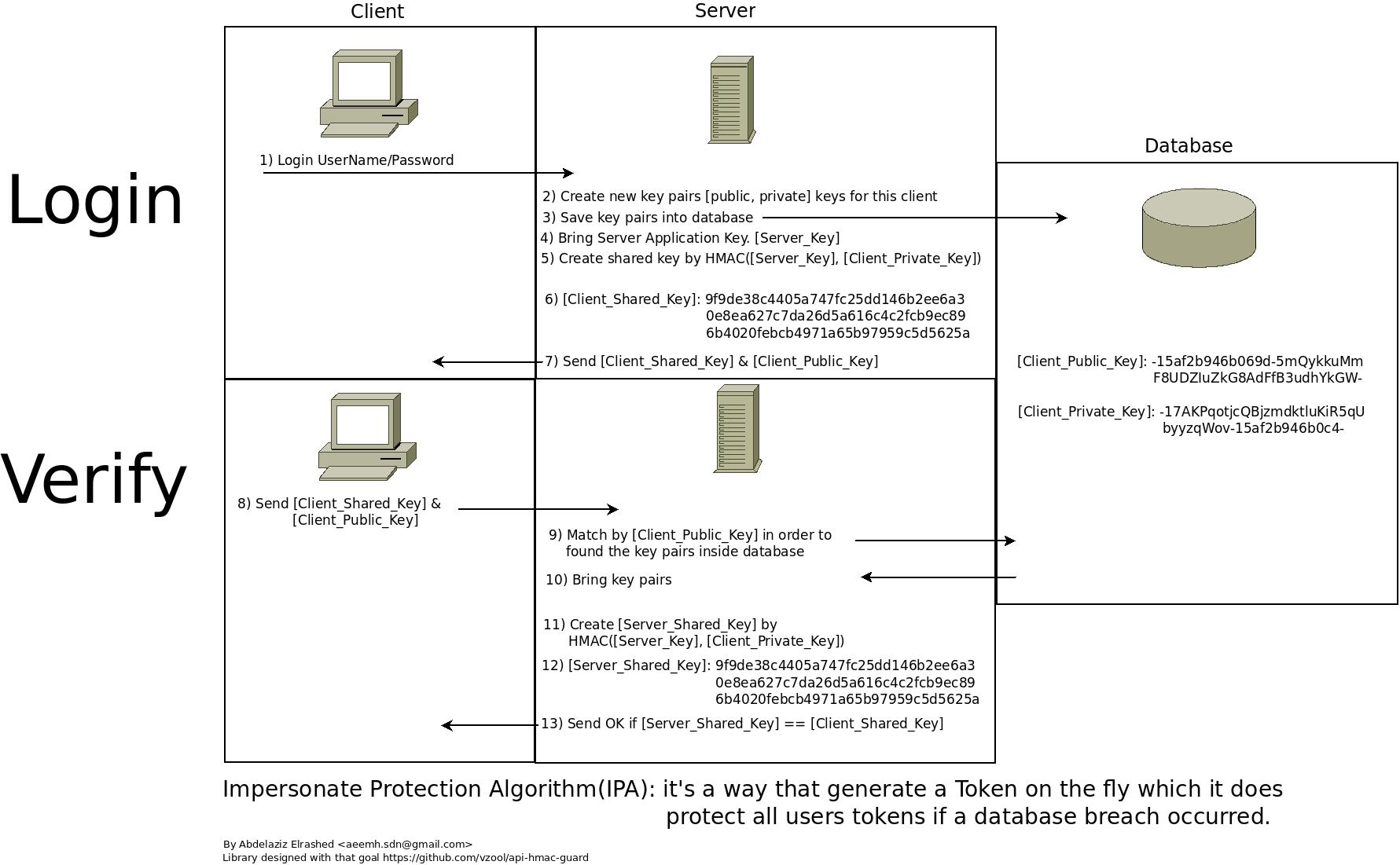
GitHub - vzool/api-hmac-guard: A simple and secure way of authenticating your RESTful APIs with HMAC keys using Laravel

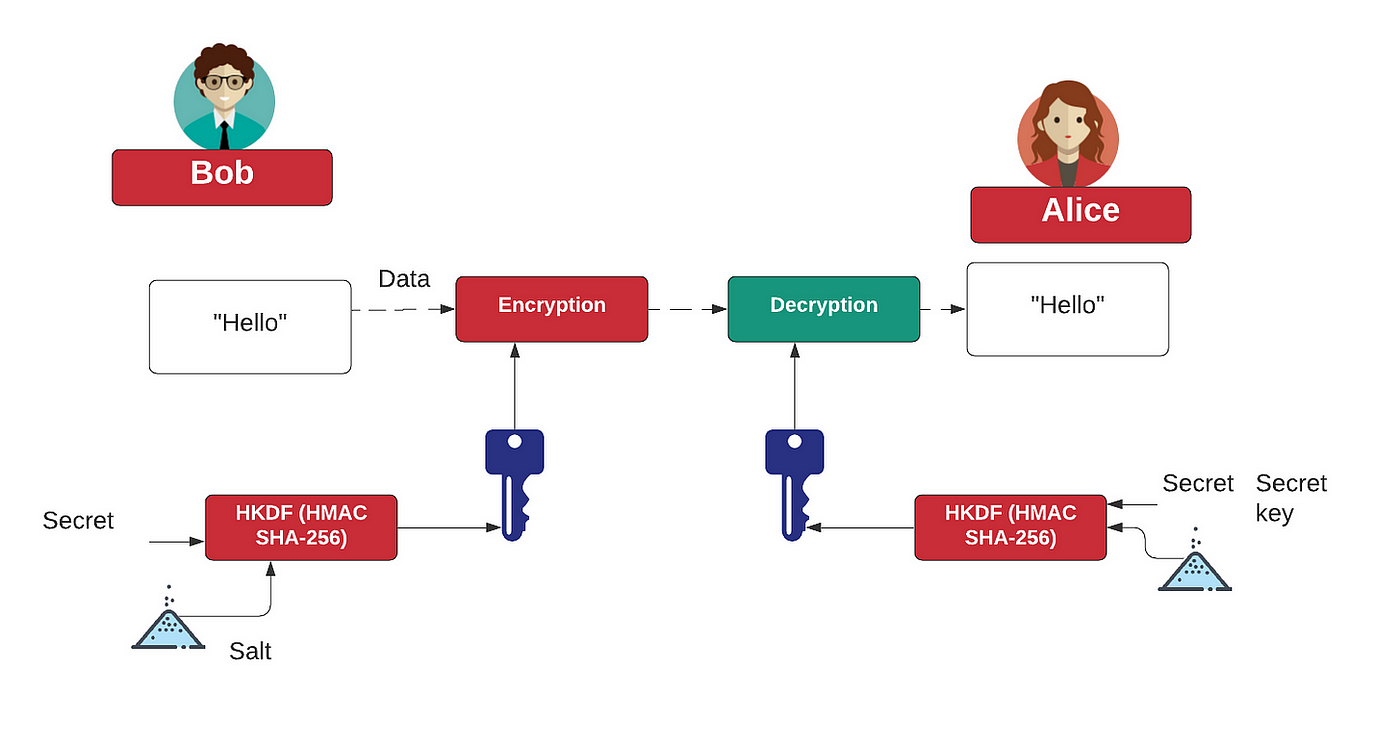
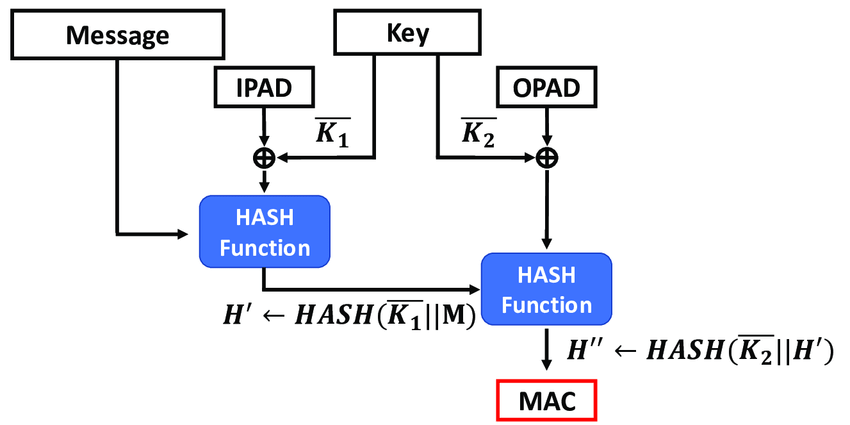
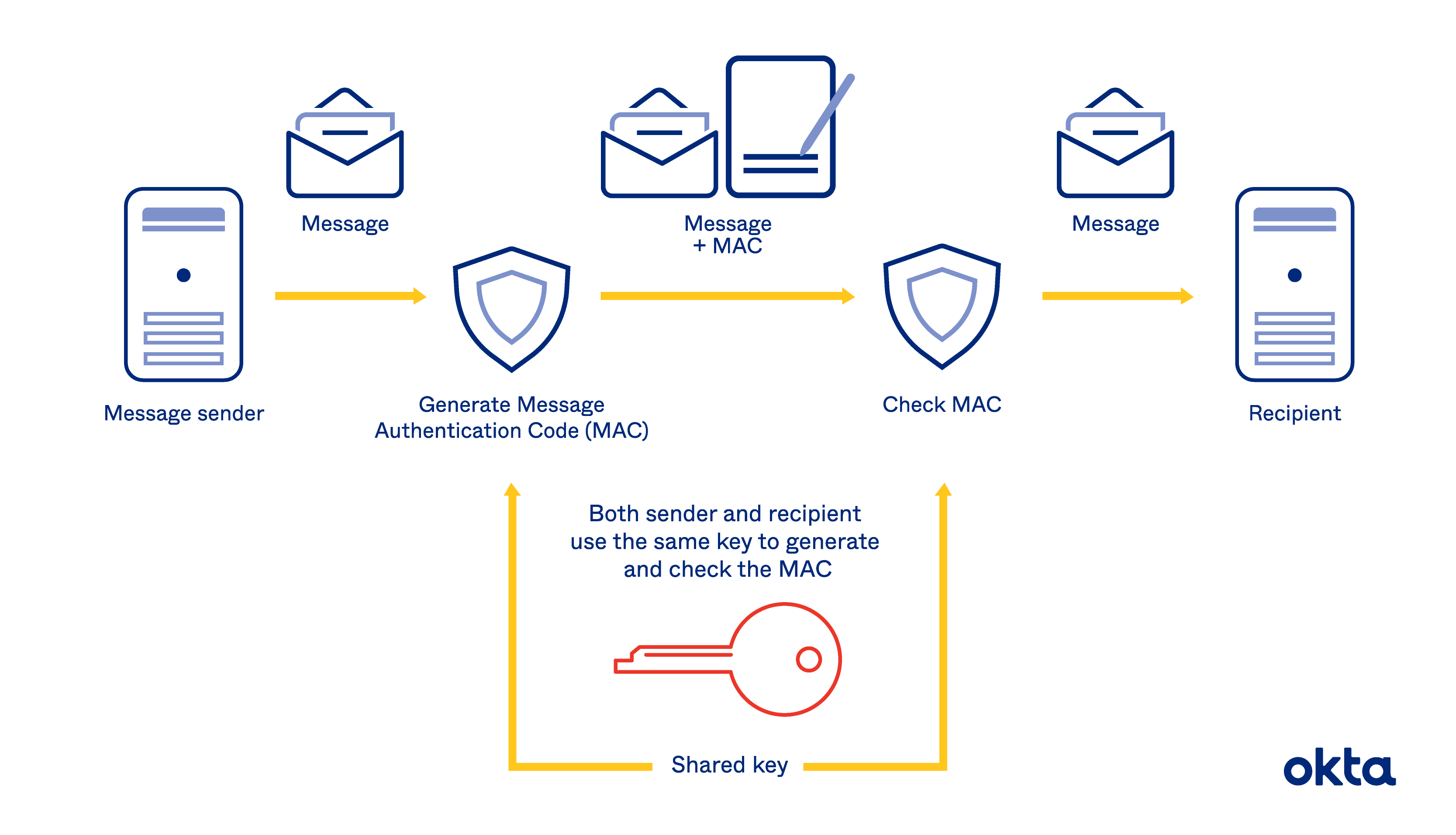
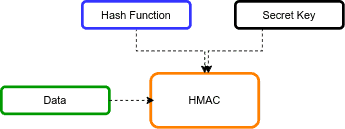
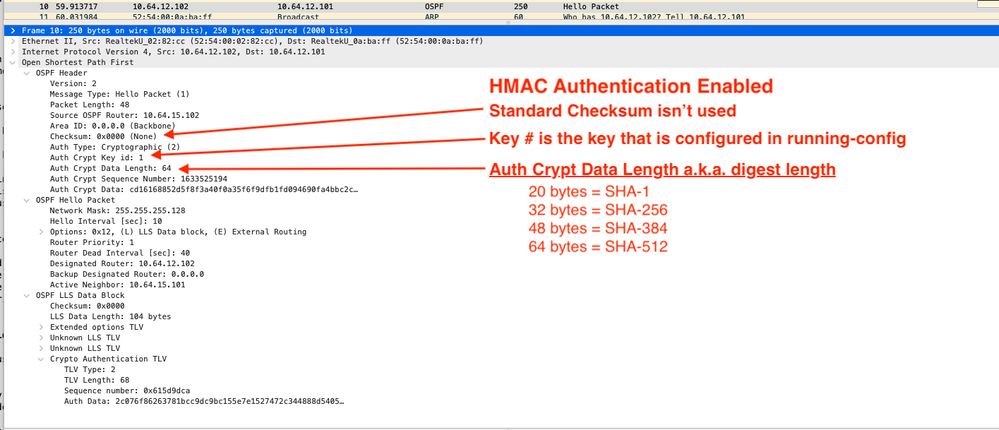
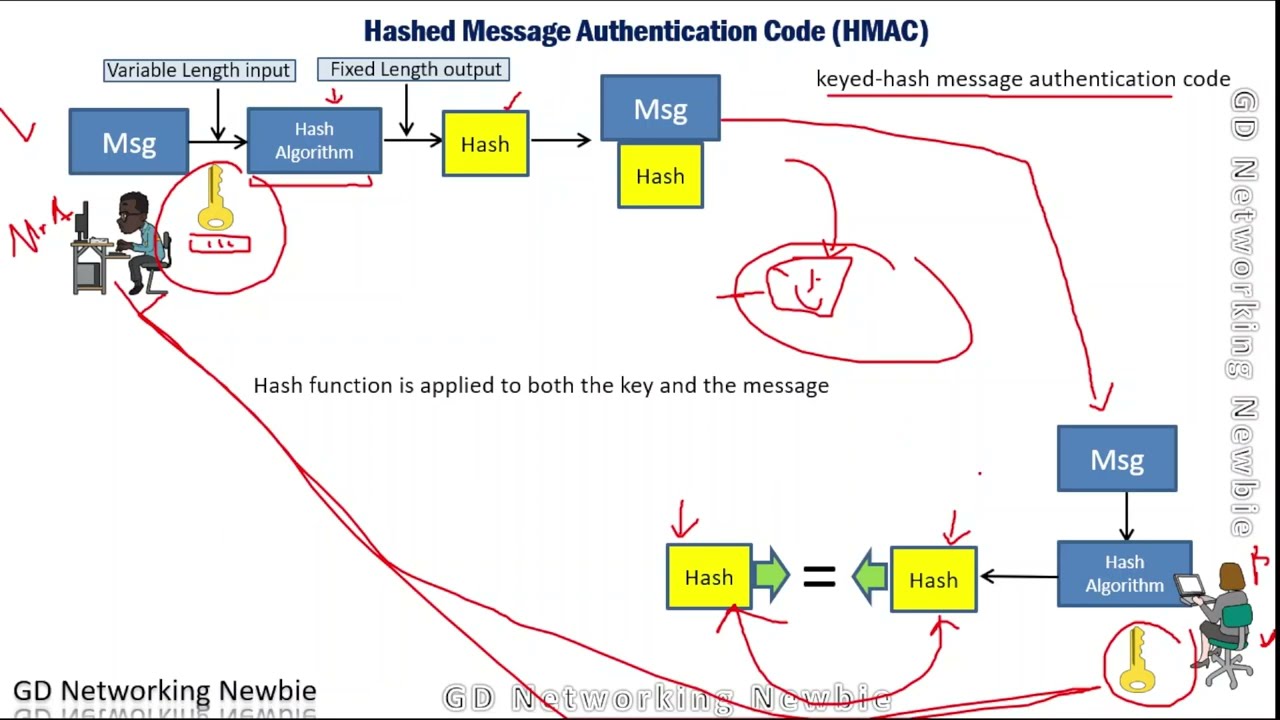
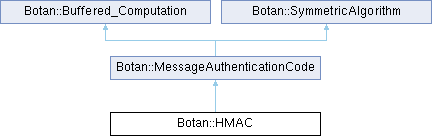
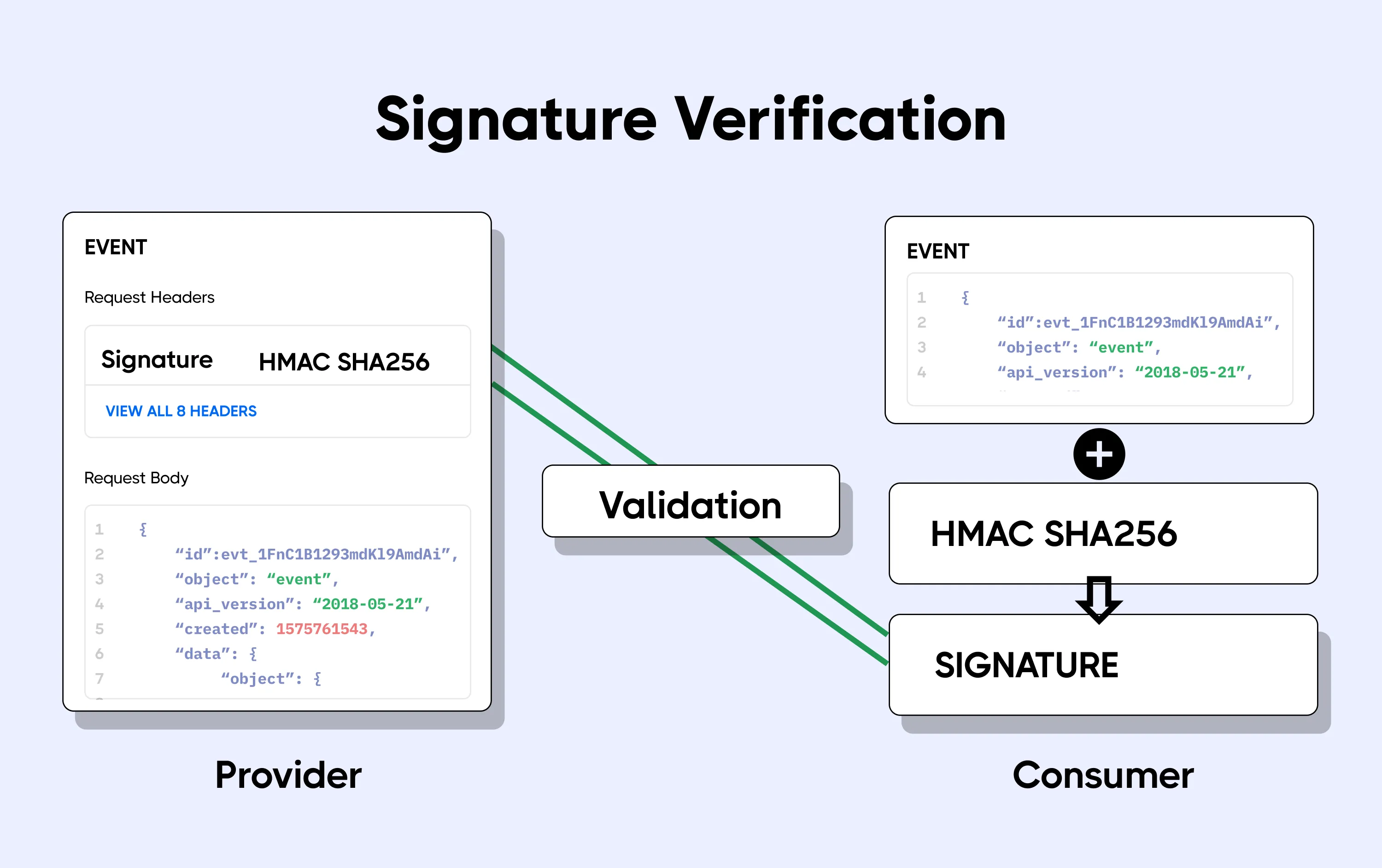
What is the HMAC message authentication system in cryptography? How to deploy it on cryptool2.1 open-source software? | by Vic | FAUN — Developer Community 🐾